
There was no particular reason that the anthropologist Robin Dunbar and the technologist Doug Engelbart ever needed to meet. Their work doesn’t need to be connected explicitly. As part of our daily struggle to survive, we constantly try to extend and augment our capabilities. Engelbart made a career of exploring the ways that personal computing could extend human capability. Dunbar established the limit against which augmentation would be applied in the social sphere.
Dunbar’s number is a theoretical cognitive limit to the number of people with whom one can maintain stable social relationships. These are relationships in which an individual knows who each person is, and how each person relates to every other person. Proponents assert that numbers larger than this generally require more restricted rules, laws, and enforced norms to maintain a stable, cohesive group. No precise value has been proposed for Dunbar’s number, but a commonly cited approximation is 150.
Dunbar’s number was first proposed by British anthropologist Robin Dunbar, who theorized that “this limit is a direct function of relative neocortex size, and that this in turn limits group size … the limit imposed by neocortical processing capacity is simply on the number of individuals with whom a stable inter-personal relationship can be maintained.” On the periphery, the number also includes past colleagues such as high school friends with whom a person would want to reacquaint themselves if they met again.
Businesses manage larger numbers of relationships through a management structure and their customer-facing employees. It’s an organizational technique developed by Daniel McCallum. If each employee can have a meaningful relationship with 150 other people, a business builds a management system around that limit. Ratios can get much higher when a business is unconcerned with the quality of the relationships, or the relationships are purely anonymous and transactional.

To increase both the productivity of employees and the quality of the customer relationships— and augmentation of human memory was required. The customer relationship management system is an extension of the salesman’s customer preferences notebook. The salesman kept reminders of what this customer or that liked or disliked. Jotted down some personal information to jog the memory for use at the next sales opportunity. This extension, or augmentation, of human memory results in better quality interactions with very large numbers of people— the required relationship information is ready-to-hand, it can be retrieved with a few keystrokes.
Once a company has become a custodian of a pool of customer identity and relationships, it has obligations to protect that data. There are now laws on the books regarding breaches of client data. Notification is required, and some form of identity fraud protection must generally be offered.
In a NY Times article on the erosion of privacy, The Electronic Frontier Foundation argues that:
…online service providers — social networks, search engines, blogs and the like — should voluntarily destroy what they collect, to avoid the kind of legal controversies the baseball players’ union is now facing. The union is being criticized for failing to act during what apparently was a brief window to destroy the 2003 urine samples before the federal prosecutors claimed them. “You don’t want to know that stuff,” she says, speaking of the ordinary blogger collecting data on every commenter. “You don’t want to get a subpoena. For ordinary Web sites it is a cost to collect all this data.”
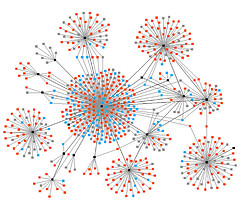
Since Malcolm Gladwell’s book ‘The Tipping Point’ we’ve become more aware of people who act as high volume hubs in social networks, so-called influencers. From a sheer numbers point of view, some of these social hubs are beginning to rival the number of connections a company might have.
As an individual gathers larger and larger pools of personal data on other people through social networks, custodial responsibilities begin to accrue. While some might say the contents of their address book belong solely to them, in the event of a security breach or a subpoena there may be some disagreement. And so now we must ask, are we our brother’s keeper?